An argumentation reasoning approach for data processing
The paper “An argumentation reasoning approach for data processing” is now published in the Elsevier Journal Computers in Industry.
Title: An argumentation reasoning approach for data processing
Authors: Erisa Karafili, Konstantina Spanaki, Emil C. Lupu
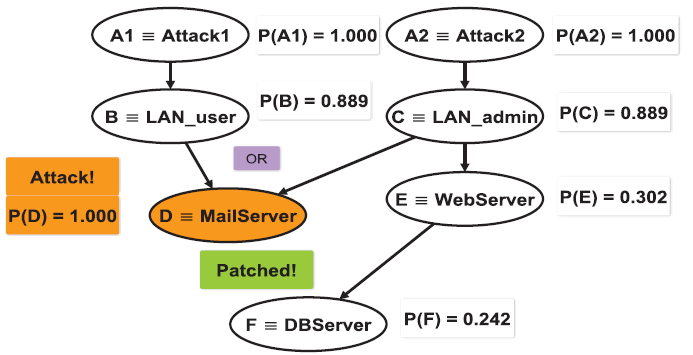
Abstract: Data-intensive environments enable us to capture information and knowledge about the physical surroundings, to optimise our resources, enjoy personalised services and gain unprecedented insights into our lives. However, to obtain these endeavours extracted from the data, this data should be generated, collected and the insight should be exploited. Following an argumentation reasoning approach for data processing and building on the theoretical background of data management, we highlight the importance of data sharing agreements (DSAs) and quality attributes for the proposed data processing mechanism. The proposed approach is taking into account the DSAs and usage policies as well as the quality attributes of the data, which were previously neglected compared to existing methods in the data processing and management field. Previous research provided techniques towards this direction; however, a more intensive research approach for processing techniques should be introduced for the future to enhance the value creation from the data and new strategies should be formed around this data generated daily from various devices and sources.
This work was supported by FP7 EU-funded project Coco Cloud grant no.: 610853, and EPSRC Project CIPART grant no. EP/L022729/1.
The paper can be found in the following link as Open Access: http://www.sciencedirect.com/science/article/pii/S016636151730338X